
Why Should You Care About SOC 2?
And by the way, ArangoDB is SOC 2 compliant!
Estimated reading time: 3 minutes

While driving along California’s Highway 101 and its billboards, compliance and SOC 2 seem to be an omnipresent – yet challenging – topic. But is it really? And if so, why? In this blog post, we want to share why and how ArangoDB has become SOC 2 compliant.
SOC 2
In short, SOC 2 is centered around how an organization protects customer data. ArangoDB is one of the leading graph databases, so working with data and protecting it from data loss and unauthorized access has been in our DNA from the start. Especially for our managed cloud platform ArangoGraph Insights Platform (formerly called ArangoDB ArangoGraph), protecting our customers’ data has been a cornerstone.
The SOC 2 certification process provided us with an independent review of our architecture and processes to keep data safe.
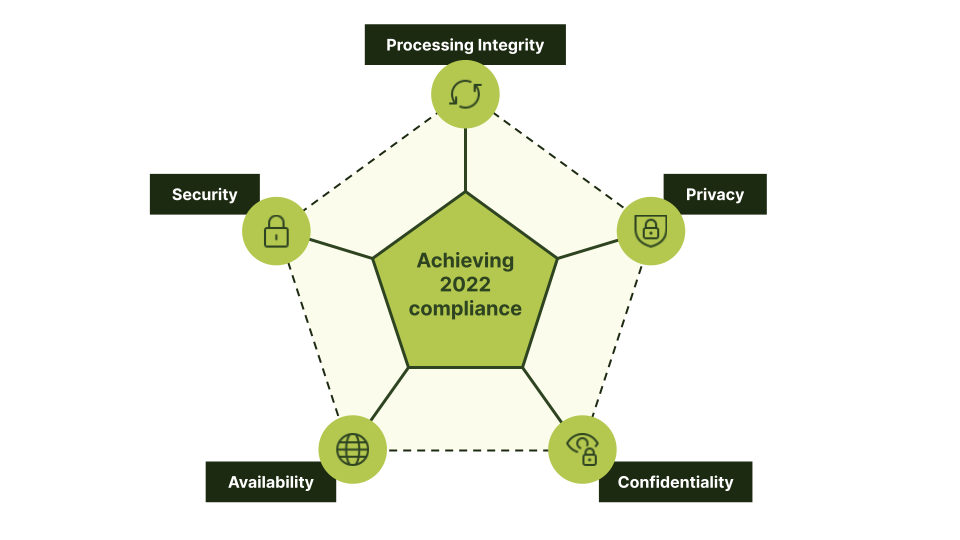
SOC 2 stands for Systems and Organization Controls 2 and is centered around Trust Services Criteria defined by the Auditing Standards Board of the American Institute of Certified Public Accountants (AICPA). These Trust Services Criteria evaluate a company’s standards in the following five areas:
- Security – Ensuring information is safe from unauthorized access.
- Privacy – Securing confidential personal information.
- Confidentiality – Ensuring the secrecy of confidential information through limitations on access, preservation, and utilization.
- Process Integrity – Continuously ensure that company processes work as designed.
- Availability – The ability of the service to be accessible and usable by authorized users when needed.
ArangoDB SOC 2 Compliance
With system processing and storage data, it comes down to trust, especially for one of your most valuable assets: data. This data includes customer data, personal information of your employees or customers, or mission-critical data necessary to keep your business running. Data is the new oil for many businesses and hence requires special attention to keep it safe and available.
Secure access is even more necessary for a managed service where the service vendor takes on the burden of managing one of the most valuable and detailed systems for large enterprises. The vendor’s primary mission is to run that service with best practices and a dedicated team, allowing you to focus on your core business without being distracted by operating a database service.
Still, you need to be able to trust the vendor with your data – without continuously evaluating the vendor’s systems and processes. This is where SOC 2 comes into play: It ensures the vendor implements security best practices and processes to keep your data safe and available.
These goals have been core to ArangoDB from the beginning, so it was the next logical step for us to have an external expert evaluate our approach and then also be able to share it with our customers. It has been a long journey, but it was less painful than the billboards might indicate, thanks to the great work of all ArangoDB team members in the past years. The security-first mindset resulted in architectural features and process improvements, including:
- Omnipresent encryption of data
- Private endpoints
- Minimal access processes
- A six-eye principle-sensitive change procedure
Big kudos to my security-focused teammates at ArangoDB!
If you are interested in more details or require access to the ArangoDB SOC 2 report, please get in touch with soc2 [at] arangodb [dot] com. To start using ArangoGraph, visit cloud.arangodb.com.
Get the latest tutorials, blog posts and news:
 Skip to content
Skip to content 